If you run a business that has any sort of reliance on computers or computer systems, you’ll have worried about your vulnerability to parties with insidious intent. More than the threat of online viruses or hackers tapping into your system remotely from a laptop like you see in the movies, phishing attacks are by far the biggest threat to small- and medium-sized businesses.
Thankfully, you don’t just have to sit idly by as your IT networks are compromised. With the help of Healthy IT, you can set yourself and your business up to minimize the risks of phishing attacks.
What is phishing?
A phishing attack involves sending an unsolicited email designed to trick a user or an entity affiliated with the target, often into installing malicious software or sharing sensitive information. Instead of using force or sophisticated techniques and technology to infiltrate your networks, phishing functions by getting someone on your side to cooperate.
Effective phishing takes advantage of aspects of human psychology such as a sense of urgency or deference to authority, and can even go by completely unnoticed. For example, an employee could receive an email that appears to come from higher-ups in your organization asking them to complete a task urgently and discreetly, such as sharing certain documents or providing pieces of information about company infrastructure or policy.
Smaller businesses are especially vulnerable to these types of attacks because they often assume that they are too small a target and get complacent with their security.
How can I stop it from happening to me?
Protection from phishing involves both prevention and mitigation. That means making it more difficult for attackers to land their attacks, and setting your business up so the consequences are minimized if they do. Here are just a few tips:
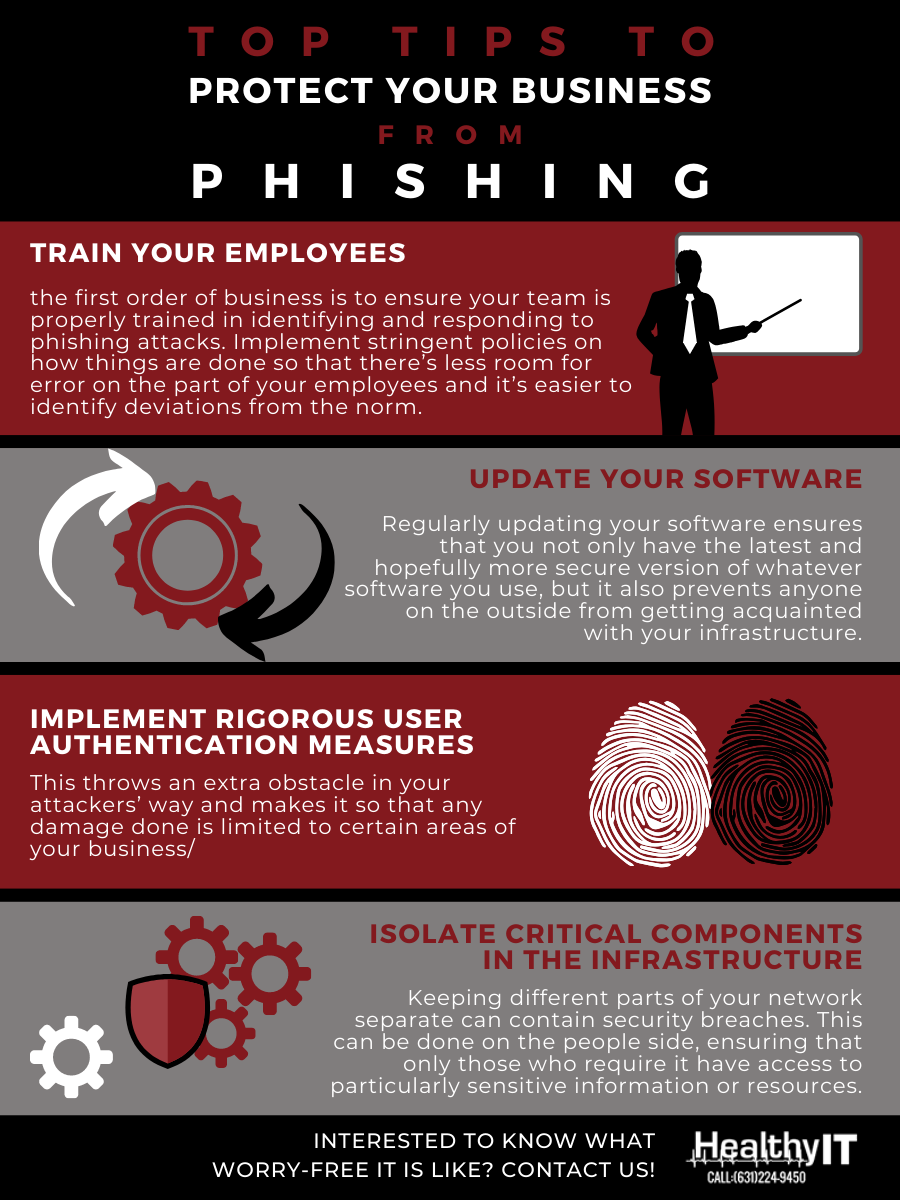
- Train your employees As phishing takes advantage of the human component, the first order of business is to ensure your team is properly trained in identifying and responding to phishing attacks. Often, this means having stringent policies on how things are done so that there’s less room for error on the part of your employees and it’s easier to identify deviations from the norm. Of course, the trick is to balance this with efficiency and morale — you don’t want security turning into bureaucracy and damaging the productivity of your employees.
- Update your software Phishing attacks usually rely on outdated software, exploiting flaws in its code. Upgrading in a timely fashion ensures that you not only have the latest and hopefully more secure version of whatever software you use, but it also prevents anyone on the outside from getting acquainted with your infrastructure. Also, don’t forget to upgrade your firewalls, email security software, and antivirus programs. These will make your device much more adept at identifying and preventing fraudulent emails from reaching your inbox in the first place.
- Implement rigorous user authentication measures
One of the most common targets of phishing attacks is login credentials for secure networks or documents. In successful cases, the attacker would usually try to use any compromised passwords in as many avenues as possible. Ensuring that these avenues are protected by different passwords throws an extra obstacle in your attackers’ way and makes it so that any damage done is limited to certain areas of your business.
For extra protection, businesses should also implement multifactor authentication — an extra security measure that requires users to enter more than one set of credentials to verify their identity. In other words, users not only have to provide passwords but also a second authentication factor like a fingerprint scan or a one-time SMS activation code. This way, if hackers manage to steal a compromised password via a phishing attack, they still won’t be able to access sensitive data unless they have the second authentication factor.Start Fighting Cyber Crime with KNOWLEDGE & ACTION!
Download our free eBook for useful tips you can use and share to your employees to protect your business from cyber crimes, data breaches and hacker attacks. Enter your details on the form on the side Share this with your employees and protect your business.
- Isolate critical components in the infrastructure Keeping different parts of your network separate can contain security breaches. This can be done on the people side, ensuring that only those who require it have access to particularly sensitive information or resources. This not only minimizes the number of available targets for attackers looking to get their hands on them, but also reduces the scope of their access if they are successful. On the technology side, this could mean keeping certain systems offline, or at least separated from others so that successful attacks are contained to those areas.
If you’re worried about phishing attacks or other cyberthreats, call Healthy IT now to protect yourself. We offer cutting-edge defenses and guidance to keep your business safe and sound. If you need our help, sign up for our free cybersecurity tip of the week to stay one step ahead of cybercriminals.

